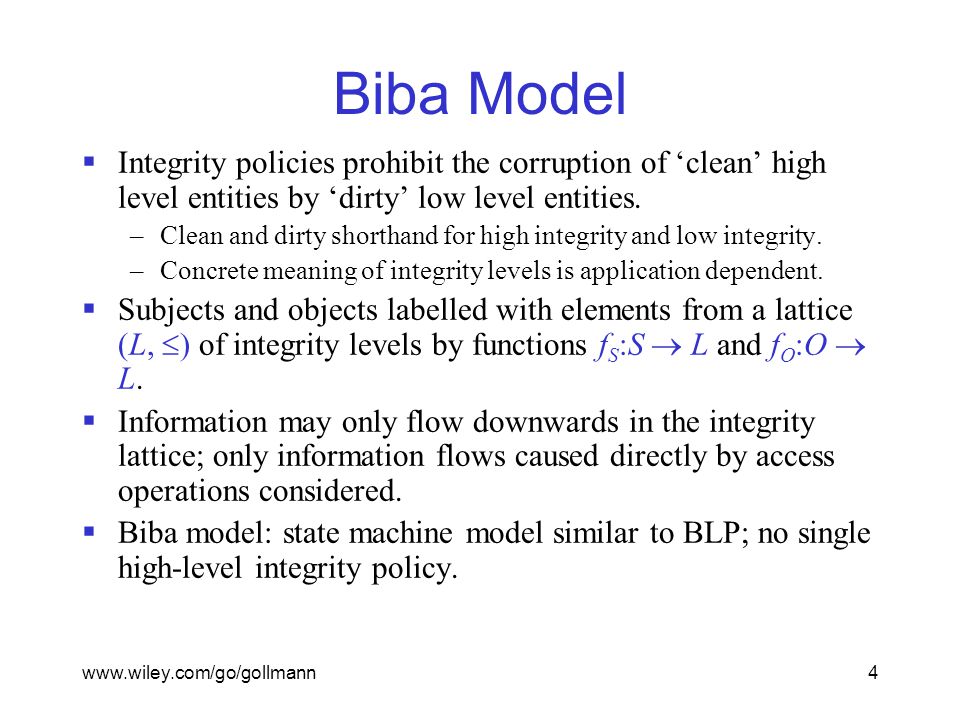
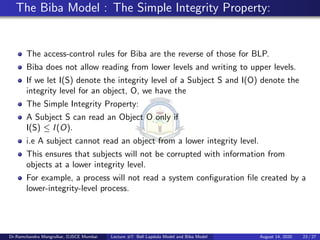
Outline Bell-LaPadula, linear case High watermark property Biba and low watermark Information-flow perspective

Improved Biba model based on trusted computing - Liu - 2015 - Security and Communication Networks - Wiley Online Library
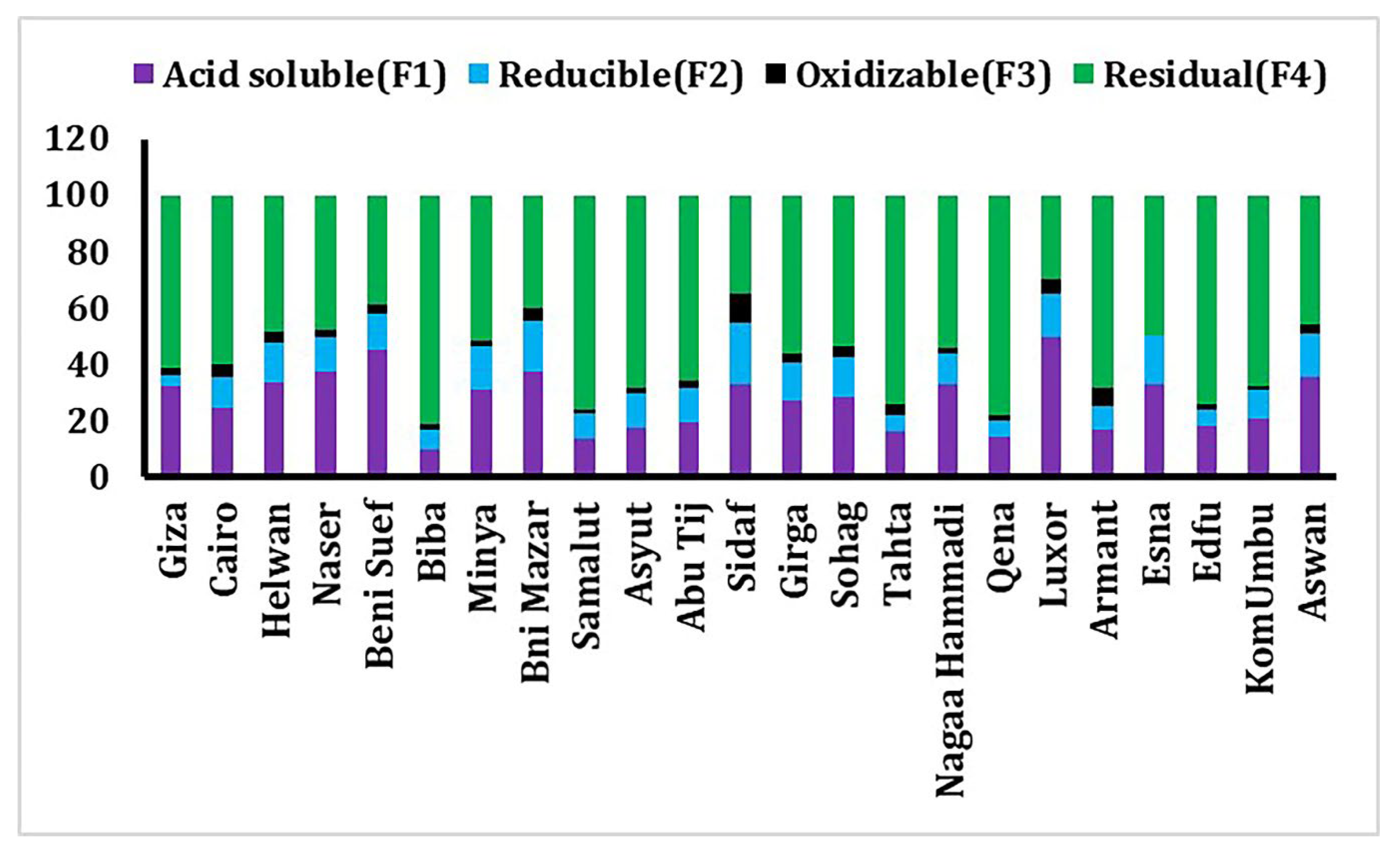
Toxics | Free Full-Text | Environmental Geochemistry and Fractionation of Cadmium Metal in Surficial Bottom Sediments and Water of the Nile River, Egypt

9 BIBA Kurta Sets From The Amazon Great Indian Festival Sale-2022 to Doll You Up This Navratri | PINKVILLA






![PDF] PRIMA: policy-reduced integrity measurement architecture | Semantic Scholar PDF] PRIMA: policy-reduced integrity measurement architecture | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/a5144e59d0a9036885b037ddacbc04effc1405e0/4-Figure2-1.png)